Data
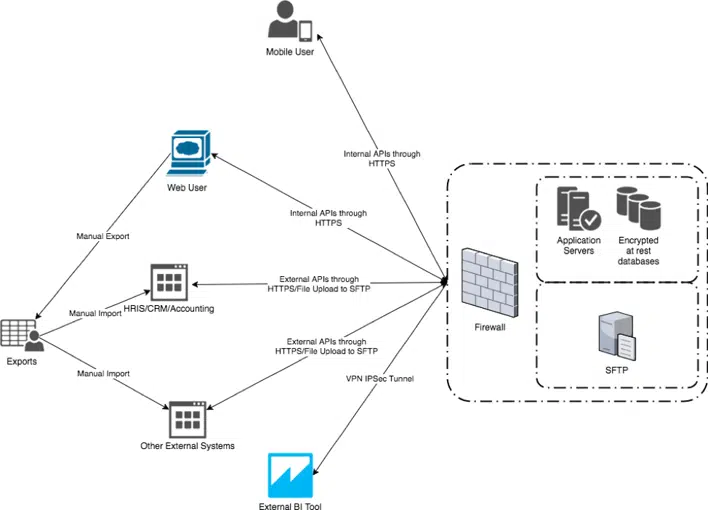
Data Flows Within a Typical AlayaCare Environment
In a typical enterprise deployment there are two main classes of users: office employees responsible for coordination, back-office, and clinical management functions who typically interact with AlayaCare via our web UI, and field workers responsible for delivering care, interacting with their schedule, clocking in and out of visits, and charting at the point of care who typically interact with AlayaCare via our mobile applications. Patients may interact with AlayaCare via our remote patient monitoring (RPM) mobile app or via our patient portal. A typical deployment may involve interfaces to HRIS and CRM software, systems of record for employee and client data respectively. Systems such as patient-facing portals may request information collected via AlayaCare software, for example schedule and chart information. Our system typically generates invoices for billing and time & attendance exports for payroll. Sometimes 3rd party business intelligence (BI) tools are connected to our data warehouse for reporting purposes.
These systems and their typical interfaces to AlayaCare’s SaaS software are shown in Figure 1 below.
Figure 1 – Systems Diagram
Data Security in Transit and at Rest
From HRIS and CRM systems to AlayaCare
Data can be exchanged either using external APIs using HTTPS or by using flat files. In the latter case, files containing data to be loaded in AlayaCare are uploaded by the external system to a SFTP server that requires authentication and presence of a SSH key on the server. Files containing data to be exported from AlayaCare are manually generated from within the software and then uploaded to the system of record.
While at rest on AlayaCare database servers
The data is encrypted at rest. The encryption keys implement the AES-256 algorithm.
Between AlayaCare servers and the web UI
The browser is stateless in the sense that no data resides locally. The software uses internal APIs using HTTPS to transfer data.
Between AlayaCare servers and the mobile applications
The mobile application uses the same internal APIs using HTTPS as the web application.
While on the mobile device
Some data can be cached locally on the device using its encrypted database. The database is destroyed on logout and the data needs to be downloaded again from the servers.
When AlayaCare’s data warehouse is accessed from the client’s BI tool
A VPN IPSec tunnel can be setup between a client and the data warehouse with limited read access to the client’s own schema.
When accessed via public APIs
The API endpoints only accept HTTPS connections and the user needs to be authenticated.
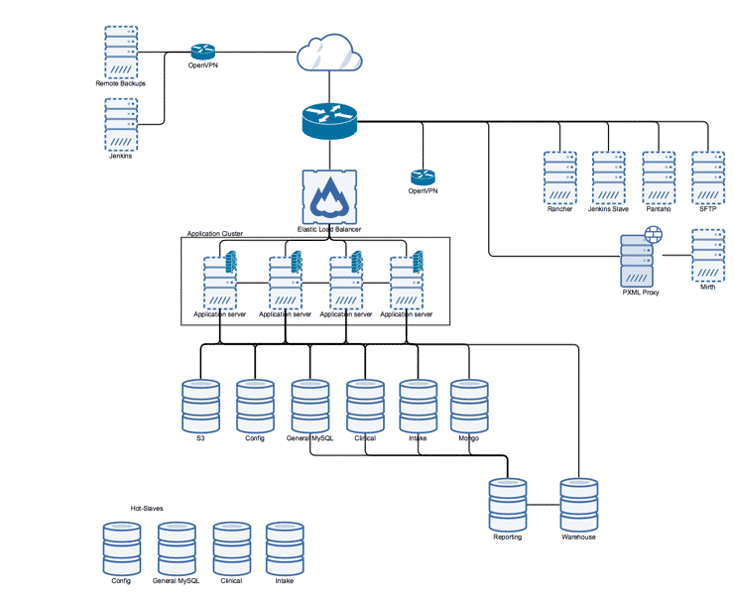
Figure 2: System Architecture Diagram
Speak to an Expert
See how our powerful home health care solution can help you increase your bottom line and improve client outcomes.